- Define the TACACS+ source interface. The source interface is usually the management interface.
ip tacacs source-interface VlanX
2. Enable aaa new model.
Tip: Before you configure your AAA commands, save your configuration. You can save the configuration again only after you have completed your AAA configuration (and are satisfied that it works correctly). This allows you to recover from unexpected lockouts as you can roll back any change with a reload of the router.
3. Define the individual TACACS+ servers
tacacs server TACACS_SERVER-1
address ipv4 X.X.X.X
key 7 0220230F5F573E0EE8EEE2D4X
timeout 5
tacacs server TACACS_SERVER-1
address ipv4 X.X.X.X
key 7 0220230F5F573E0EE8EEE2D4X
timeout 5
4. Define the TACACS+ server groups
aaa group server tacacs+ TACACS_SG
server name TACACS_SERVER-1
server name TACACS_SERVER-2
5. Define the aaa authentication method list
aaa authentication login AAA_VTY group TACACS_SG local
aaa authentication login AAA_CONSOLE local enable
6. Define the aaa authorization method list
aaa authorization exec AAA_VTY group TACACS_SG local if-authenticated
aaa authorization commands 0 AAA_VTY group TACACS_SG local if-authenticated
aaa authorization commands 1 AAA_VTY group TACACS_SG local if-authenticated
aaa authorization commands 15 AAA_VTY group TACACS_SG local
- Define the aaa accounting method list
aaa accounting network AAA_VTY start-stop group TACACS_SG
aaa accounting exec AAA_VTY start-stop group TACACS_SG
aaa accounting commands 0 AAA_VTY start-stop group TACACS_SG
aaa accounting commands 1 AAA_VTY start-stop group TACACS_SG
aaa accounting commands 15 AAA_VTY start-stop group TACACS_SG
- Apply the AAA list to the virtual line (SSH console)
line vty 0 31
authorization commands 0 AAA_VTY
authorization commands 1 AAA_VTY
authorization commands 15 AAA_VTY
authorization exec AAA_VTY
login authentication AAA_VTY
- Apply the AAA list to the console port
line con 0
exec-timeout 15 0
privilege level 15
login authentication AAA_CONSOLE
10 . Enable HTTPS AAA
ip http authentication aaa login-authentication AAA_VTY
ip http authentication aaa exec-authorization AAA_VTY
ip http authentication aaa command-authorization 15 AAA_VTY
ISE Config




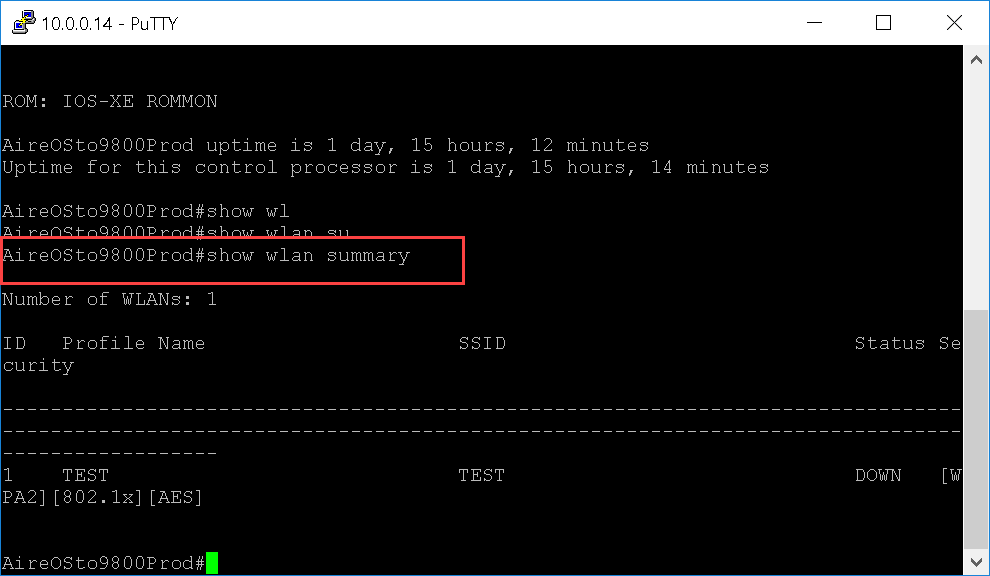
Test GUI



Test CLI


Test helpdesk / jradmin



test helpdesk / jradmin – CLI


If the policy is to restrictive edit command set and tacacs profile/shell


